Featured Photo by FLY:D on Unsplash
There’s an important choice to be made when managing application security risks today: Remediate security issues early in pre-production or pay more to fix them in production while hoping you don’t get compromised or attacked. For Bob Durfee, head of DevSecOps at Takeda Pharmaceutical, the choice is simple: He’s determined to resolve security issues in 10 minutes during the pre-production phase of application development instead of taking weeks to remediate the same issues in production.
- Learn what’s emerging on the threat horizon from both hacker and defender points of view.
- Find out how your peers are transforming their SOC using automation.
- Get tips and tricks to improve your threat detection and investigation skills.
- Learn industry best practices to bring back to share with your team and peers.
- Hear from special guest speaker Brian Krebs, leading Cybercrime Journalist (krebsonsecurity.com)
Read DevOps.com Newsletter July 24, 2022
Remember when ransomware was the main security threat that DevOps teams needed to worry about? Those days are over. Ransomware attacks are certainly still happening, but API security breaches—which increased by a whopping 600% in 2021—are now poised to become the top attack vector for threat actors, according to Gartner.
That’s the bad news. The good news is that, in many respects, the security practices that DevOps teams already have in place to defend against ransomware can be repurposed to deliver API security, too—with a few tweaks. And API analytics can help, too, by measuring things like user experience to determine where the relationship between end user and application fails or is insecure.
Four steps to avoiding a cloud cost incident, what the new OWASP top 10 changes mean to devs, survey sees alternative cloud service providers gaining ground and more!
Contents:
- Upcoming Events
- CPE Webinar:
- How to Effectively Communicate Cybersecurity Risks to the Board
- AT&T Cybersecurity Update 30 June 2022
- Exterro E-Discovery Defence
- Events by DevOps Institute
- Major Cybersecurity Events
- Everbridge: AI & ML in Security
- Palo Alto Networks:
- Key Cybersecurity Players
- May 2022
- AT&T Cybersecurity
- IT GRC Forum
- Palo Alto Networks
- Veeam Backup & Monitoring
- Security Boulevard
- GitLab has been a catalyst for change when it comes to the evolution of DevSecOps versus traditional application security testing.
Upcoming Events
CPE Webinar:
How to Effectively Communicate Cybersecurity Risks to the Board
August 25th @ 1pm EST
It has always been challenging for security leaders to communicate the value of cybersecurity investments to board. Giving transparency about the weakness of organizations can be pretty uncomfortable but, it is essential to increase the Cybersecurity level. Attend this webinar to learn how to improve your board’s cybersecurity posture by effectively communicating risks in business terms, including how to:
- Create trust with dialogue delivery and engage leadership by categorizing in financial terms
- Use data to explain the problem, and share how that same data provides you with a way to solve it
- Connect the dots between enterprise risk and environmental, social and governance (ESG) agendas
- Help board executives move to an ‘internet everywhere’ approach
- More IT events via BrightTalk
- Save Your Seat
| — LIVE WEBCAST — |
| Is Your Business Secure Enough to Work at the EdgeWEDNESDAY, JULY 13TH @ 1:00 PM CT |
| The world is moving to edge computing. Take a look around at how you live and work today. Chances are you living in a hybrid world with everything from how you work to how you shop to how your business operates its manufacturing environments. All of this is made possible because of edge computing.Regardless of where you are on that edge journey, you need to think about securing how you work, how you shop, and how your business runs. Cyber threats run rampant in today’s digital world.As you and your business prepare for the new digital world of edge, how can you advance your business goals while acting with confidence with the reality of cyber attacks looming at every seemingly possible step? How do you safeguard your digital assets to deliver strong business outcomes? Join us to gain insight into: |
| What edge computing is and means to your business How organizations are preparing for cybersecurity in an edge environment Why traditional cybersecurity practices are evolving and include a focus on Zero Trust |

Identity and access management (IAM) are now at the core of any approach to building and maintaining a zero-trust IT environment. Often viewed as the last mile of security, it turns out that modern security now starts with the ability to verify the identity of not just people but also applications and even machines.
IT teams, of course, have been relying on directories to manage access for years. IAM platforms, however, take cybersecurity to the level required to combat, for example, ransomware attacks that at their core compromise identities to not just disrupt, but rather, paralyze organizations.
Register now to learn how to leverage IAM platforms to protect your organization from serious attacks.

Enterprises and cloud-native organizations around the world have gravitated to Kubernetes for powering their applications and tech stacks. Why? Kubernetes provides users with always-on orchestration of their microservices-driven applications.
As security teams partner with DevOps teams to secure their applications, organizations have a lot of security requirements to consider, including vulnerability management of their hosts and applications, secure networking, access control measures and more. At the same time, DevOps workflows provide many new ways to integrate security in an automated fashion.
In this webinar, Orca Security’s Keith Mokris and Jacob Graves will explain:
- Kubernetes architectures and how microservices are the new way of running applications
- Security controls that are vital for protecting Kubernetes at scale
- The latest trends and survey data from Techstrong Research


Kubernetes security is becoming more challenging as the number of clusters running cloud-native applications continues to multiply rapidly. Challenges range from allowing in only legitimate traffic and enabling least-privileged communications between services to defend against attacks moving laterally between clusters, to validating how a workload is operating within the expected guardrails.
It’s also often assumed that because a container only runs for a few seconds on a
Kubernetes cluster, it won’t be compromised. However, containers are starting to run for longer periods and are being used with stateful applications containing sensitive data. Organizations also are paying more attention to Kubernetes as they look to lock down software supply chains in the wake of a series of high-profile breaches.
As Kubernetes becomes ever-present in production environments, it is imperative that organizations understand and take appropriate steps against the threats. In this editorial webinar, our panel of experts will discuss:
- The state of Kubernetes security
- What organizations need to address with respect to Kubernetes security in production environments
- Who should be in charge of Kubernetes security in the age of shift-left
AT&T Cybersecurity Update 30 June 2022
Remote workforce solutions from AT&T, powered by Palo Alto Networks, provide highly secure access to resources hosted in the data center, the internet, or private and public clouds.
Remote workforce solutions use a cloud-based infrastructure to deliver a suite of security and networking services for remote users. Organizations benefit from a single pane of glass that sets up the connectivity that cybersecurity employees and contractors need, including:
- VPN options
- Firewall as a service (FWaaS)
- Zero Trust network access (ZTNA)
- Secure web gateway (SWG)
- ML-powered threat prevention
- Domain name system (DNS) security
Exterro E-Discovery Defence
- Document review isn’t just for e-discovery anymore. Between data subject access requests, incident and breach response, and internal investigations, organizations must have defensible, compliant document review processes in place before they need them. The keys to defensibility, as this quick guide demonstrates, are repeatability, consistency, and efficiency.
- Ransomware attacks, malware incidents, and data breaches happen every day. With ethical and legal duties to protect clients’ information, law firms and legal service providers (LSPs) must be prepared to respond to a data breach with a timely, efficient response plan.
- How to establish e-discovery defensible processes: we seek to pull together best practices and tips from those who are most intimately involved in the e-discovery process. We’ll cover all of the key areas that in-house legal teams want to consider, and you’ll hear from e-discovery managers, attorneys, and federal judges on what to look out for so that you can become a Master of E-Discovery.
Events by DevOps Institute

After the phenomenal success of SKILup Festival: Denver, we are heading to London to bring you the only in-person event that empowers the people, who power IT.
Come to SKILup Festival: London and surround yourself with the best in the DevOps industry.

Attend this in-depth, hands-on workshop with a Calico expert to design and implement security controls, observe the workloads’ security posture and perform advanced troubleshooting for your containerized workloads running in self-managed Kubernetes in AWS or EKS. The 90-minute interactive lab comes with your own provisioned Calico Cloud environment and is designed to provide more complete knowledge on:
- Quick vulnerability assessment and management for build time
- Reducing attack surface with zero-trust workload access controls
- Implementing host isolation with identity-aware microsegmentation
- Runtime visualization, anomaly detection and live troubleshooting of microservices
Major Cybersecurity Events



As the pandemic continues to affect both business and personal lives, expectations of a ‘return’ to pre-pandemic conditions have faded from most plans. Underlying trends that have always driven information security, such as new technologies, greater compliance mandates and more severe security incidents, continue to be significant change agents. The 2022 Thales Data Threat Report, based on data from a survey of almost 2,800 respondents from 17 countries across the globe conducted by 451 Research, part of S&P Global Market Intelligence, reviews and analyzes these trends and changes.
Many organizations continue to be unprepared for the security challenges of diverse threats, ransomware, accelerating cloud transformation and hybrid work. In fact, according to the report’s survey 21% of all respondents said they had experienced a ransomware attack. Furthermore, 22% of respondents worldwide said they have paid or would pay a ransom for their data.
This webinar will review the changing landscape of data security risks and threats. Specifically, you can expect to learn about:
• Leading sources of data threats
• Ransomware preparedness and how it has changed breach economics
• Breaches and their impacts weigh on security planning
• Data sprawl’s impact on data security
• Cloud usage trends and security practices in the cloud
• Threats of remote and hybrid workforces
• Future threats such as quantum computing

Traditional application security tools are not solving today’s problems and traditional tools can create more problems than they solve. False positives are all too common and overwhelming and they can also be as time consuming as actual attacks. Join this discussion to gain insights on how you can use modern security strategies and tools to help minimize disruption, prevent bottlenecks, and more.
Your Cyberattack Response In 10 Critical Steps
28/06/22 10:00AM CEST

Nebula Stops Evasive Threats in Real Time
Welcome to our Tech Deep Dive Miniseries where you will learn about Nebula, a series of network security innovations that add inline deep learning and harness the processing power of the cloud.
PAN-OS® 10.2 Nebula collects, analyzes and interprets potential Zero-Day threats using deep learning in real time – an industry first. This results in 6X faster prevention and 48% more evasive threats detected than any previously available solution.
In this highly-interactive six-part miniseries, you’ll meet Palo Alto Networks security experts and get their unique insights and advice on the continuously evolving cybersecurity threat landscape.
Troubleshoot Remote Worker Challenges at Lightspeed
July 13, 2022 | 12 PM EDT
Join this webinar to learn how ADEM on Prisma® SASE helps IT teams troubleshoot challenges within today’s hybrid workplace. Hear stories from IT teams who have helped make their organizations more efficient with Autonomous Digital Experience Management (ADEM) and the full entire service delivery path visibility it provides.
Achieve better security outcomes
Zero Trust removes all implicit trust and continuously validates every stage of a digital interaction. To evolve into a true Zero Trust Enterprise, policies and controls must apply across users, applications and infrastructure to reduce risk and complexity while achieving enterprise resilience.
Keep an eye on these cyber trends
“Now is the time to counteract professional cybercriminals, and to secure data and systems by minimizing human security risks!” Niklas Hellemann SoSafe

Everbridge: AI & ML in Security
Grandiose claims about the ability of AI platforms to eliminate the need for security analysts have given way to more rational assertions that focus on the role machine learning algorithms will play in augmenting the skills—and easing the strain on—cybersecurity professionals. Now, it isn’t so much about whether AI will replace cybersecurity professionals as it is about how quickly AI models based on machine learning algorithms can be applied to help thwart attacks.
Palo Alto Networks:
The most recent techniques used by hackers today to gain access to your data, and what you can do to minimize your risk:
- Lateral Movement Attacks executed within Public Cloud
- Social Engineering Attacks and what are the 3 most important things you need to know about it
- User Identity Compromised Attacks – we’ll share a few valuable tips that can help safeguard your company
Key Cybersecurity Players
Palo Alto Networks – Leader in Global Cybersecurity
IT GRC Forum – Cybersecurity Intelligence
Data Security and Compliance Powered by Veeam
Security Boulevard – home of the Security Bloggers Network (SBN). A single source for news, analysis & education on issues facing cybersecurity industry.
Synopsys – next-gen application security (AppSec) starts with implementing a robust application vulnerability correlation (AVC) solution.
Sosafe/Forrester – Human Risk Review 2022 Report
DevOps Institute – a professional member association and certification authority. The mission is to advance the humans of DevOps.
DevSecOps – Security as Code Manifesto.
DevSecOps Solutions & Services:

- RedHat integrates DevSecOps into Kubernetes environments
- Devon – everyone is responsible for security
- Snyk integrates security objectives as early as possible in the lifecycle of software development
- Plutora builds governance into engineering workflows
- Aqua – Real-life DevOps security challenges
- JFrog – Security vulnerabilities, license compliance issues
- GitLab – “shift left” to find security vulnerabilities earlier within DevOps
- Xmatters – cloud-native DevOps and CloudOps security deployments

Register and select any pass level to access our exclusive in-person event.
*Use code 52UTECHSTRONGXPO to obtain your FREE Expo Pass!
Gain valuable information on the hottest DevOps and cybersecurity topics.
• Meet and exchange ideas with internationally recognized leaders from the Linux Foundation, CNCF, Target, Red Hat, Contrast Security, Cobalt, Intel and many more.
• Get expert advice and tips on how to build a modern cybersecurity practice within your company.
May 2022
AT&T Cybersecurity
72% of respondents from a 2021 global survey reported that they have plans for adoption of zero trust in the future or have already adopted it.
Three essential elements for zero trust success:
• Principle #1: Connect users to applications and resources, not the corporate network
• Principle #2: Make applications invisible to the internet, to eliminate the attack surface
• Principle #3: Use a proxy architecture, not a passthrough firewall, for content inspection and security
Zero trust provides the foundation for cloud-first organizations to accelerate digital
transformation and empower employees to work productively and securely from anywhere:
- First, select a platform that uses identity and business policy to establish trust, and connects users to resources without placing them on the corporate network.
- Second, protect applications by making them invisible to adversaries and accessible only by authorized users.
- And finally, use a proxy architecture, not a passthrough firewall, to secure data and ensure effective cyber threat protection.


IT GRC Forum
- European Union Agrees New Cyber Security Legislation
- CISA says unpatched VMWare devices should be considered to be compromised and urgenty need to be checked
- Never Trust Anything Again – The Zero Trust World
- Vishing (voice phishing) cases have increased almost 550 percent over the last twelve months, with hundreds of thousands of cases detected
- Data Storage Is the Number One Cyber Recovery Strategy – Create multiple backups of your files, keeping your business safe from major data disasters
- Trojan Malware: Inserting malicious links into phishing emails allows attackers to harvest usernames, passwords & bank details from Windows users
- App stores share a common threat profile and the fact that some apps come loaded with malware presents an immediate risk to millions of unsuspecting users
- Google is giving users much more control over personal privacy and the adverts they are served, as well as better security for online payments
- Britain’s financial regulator is warning people to beware of fake financial advisers offering investment schemes via online meeting platforms.
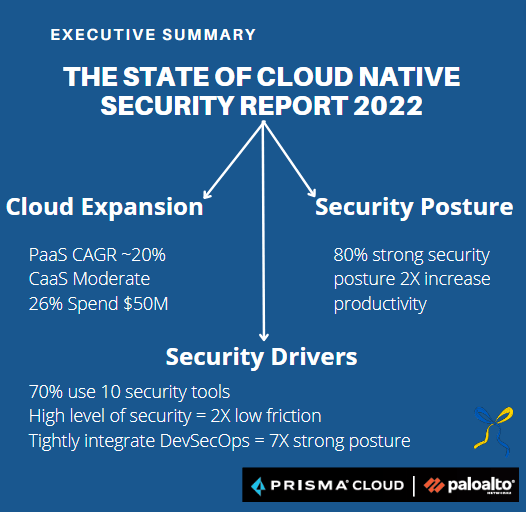
Palo Alto Networks
- Zero-Trust Enterprise
- Cloud-Native Security
- Security Operations
- Threat Intel & Consulting
- ML-Powered Network Security
- Cloud Delivered Security
Securing Your Digital Transformation
There are key steps in this process:

Cyberpedia Your Source For Understanding Cybersecurity
Veeam Backup & Monitoring
- 2022 Ransomware Trends Report: Are you ransomware resistant?
- Security everywhere with Kasten K10 v5.0
- Security everywhere, from development to deployment
- Ecosystem advancements from procurement to operations
- Shifting data protection left
Security Boulevard
Problem: Regardless of your company’s size or industry, migrating to the public cloud and Kubernetes is fraught with business and technical risk.
Solution:
- Managing the full life cycle of Kubernetes clusters
- Applying curated blueprints to clusters
- Securing developer and SRE access to clusters across hybrid environments
- Applying the requisite level of governance and control
Synopsys Portfolio – Maintain velocity without compromising security

GitLab has been a catalyst for change when it comes to the evolution of DevSecOps versus traditional application security testing.
| Process | Old | New |
| Security testing | Security testing is performed by security pros, using their own tools, usually at the end of a development cycle. | Security testing is automated within the CI pipeline with findings delivered to the developer while they are still iterating on their code. Findings are limited to new vulnerabilities introduced in this code change making it highly clear and actionable for the developer to correct the security flaws that they created without taking responsibility for the backlog of flaws and technical debt that already existed. |
| CI and security | CI scripts might be used to call security scanners and pull the findings into the CI pipeline. Yet the two tools remain separated. Often elements are missing and integration must be maintained. Licenses of the CI tool and the scanners are separate and can be difficult to manage, especially when they charge by different variables (users, apps, code size). | United into a single tool, there is no costly integration to maintain and only a single license to manage. |
| Remediation | Security pros must constantly track remediation status of critical vulnerabilities (risk). The findings are in one tool, but the remediation effort is within the development team putting the two teams in a constant state of friction and inefficient communications. | By sharing a single tool, security pros can see the status of remediation for given vulnerabilities right in their dashboard. And, when GitLab issues are used, both teams can collaborate to work together on remediation. |


Leave a comment