Oracle DevRel Team:
Oracle University is excited to offer free training and certification for Oracle Cloud Applications Business Processes starting June 1 through August 31, 2023.
It’s a great time to get Oracle certified with:
- Training and certifications covering end-to-end business flows across Human Capital Management, Sales, Procurement, Financials and Supply Chain – enabling you to explore, plan, implement and test Oracle Cloud Applications.
- A vibrant community that fosters collaboration, idea-sharing, and professional development.
- Prizes and badges for completing various learning milestones in our Race to Certification challenge.
Plus, access free training and certification across Oracle Cloud Infrastructure and Data Management.

Attain in-demand skills across OCI, AI, Machine Learning, OCI multi-cloud, data management, applications business processes and earn badges and win prizes for free.
Join aspiring software engineering professionals to learn how to build a career as a software engineer; why you should become a software engineer, skills that every software engineer should have, skills based learning for software engineers, a day in the life of a software engineer and the future of software engineering.
Are you aspiring to become a software engineer? In this free online event, you will receive insights from from renowned companies, software engineers and tech professionals on how to successfully develop and navigate your career path in software engineering.
The event will be live-streamed and you are free to join specific sessions or the full programme!
This event is organised free of charge by European Leadership University
MATLAB EXPO 2023 Proceedings
- How Siemens Energy Enables the Global Energy Transition
- Hands-on workshops: Using MATLAB with Python; Using Autonomous Drones to Detect and Track Wildfires; Interactive Learning with MATLAB Apps and Live Scripts
Table of Related Contents Below:
- AI Related Events 2023
- DevOps Webinars 2023
- Best of 2022:
- Crypto
- Digital Marketing Week Ahead 11 Dec ’22
- Cloud-Native Week Ahead 11 Dec ’22
- #StocksToWatch Wed 23 Nov ’22
- EdTech Q4 2022
- Upcoming Tech Events of Interest
- Coming Up This Tech Week (W, 12 Oct. ’22)
- E-Discovery Day Dec ’22
- BrightTalk Weekly Oct ’22
- DevOps Weekly Oct ’22
- Tech Weekly Sept ’22
- Marketing Digest Sept 2022
- EdTech Update Aug 2022
- Logistic Regression Practical Case Study: Breast Cancer detection using Logistic Regression
- Python for Finance: Enroll in our Python for Finance course today! Learn to use various Python libraries such as QuantConnect to perform financial analysis and research.
- Deep Learning with Tensorflow and Keras: Enroll in our Deep Learning with Keras and Tensorflow Course! Learn how to use Python for Deep Learning with Tensorflow 2 and Keras libraries. Start today!
- Cybersecurity Update July 2022
- DevSecOps Monthly Picks July 2022
- ML/AI Credit Card Fraud Detection
- Q2 2022 Update
- Tech Week Ahead Monday, July 11, 2022
- Events
- E-Training Opportunities
- Cybersecurity Monthly Update – May 2022
- A Weekday Market Research Update
- Coming Up This Week
- Hey there!
- New posts in your inbox
AI Related Events 2023
| Cypher 2023 |
| India’s Biggest AI Summit 11-13th Oct 2023Hilton Convention Center, Manyata Tech Park, Bengaluru Cypher 2023 is presented by Shell and Powered by Fractal & Genpact. Mark your calendars for October 11-13, as Cypher 2023 is set to take the stage as India’s largest and most impactful AI summit. Since its inception in 2015, Cypher has served as the definitive platform for bringing together a diverse range of stakeholders—from enterprises and academia to industry luminaries and groundbreaking innovators. This year’s summit offers unparalleled networking opportunities, allowing you to engage with top-tier leadership and build meaningful connections that can propel your career and business forward. With over 100 speakers participating in more than 80 sessions, the event promises a rich tapestry of discussions covering a wide array of topics, including data science, machine learning, and AI. Regular Passes to Expire on 22nd Sep Book Passes |
Become a HashiCorp Certified Cloud Engineer
San Francisco & Online | October 10-12, 2023
Join cloud engineers, platform teams, thought leaders, and executives from around the world for 2+ days of conversations on the future of cloud automation. Register now for your pass to hands-on learning, certifications, product news, and more.

NICE continues to revolutionize CX for employees, consumers, and brands by launching the next generation of Enlighten at Interactions 2023. Enlighten combines generative AI and CXone’s vast array of CX data to deliver a trusted, purpose-built, conversational AI experience for businesses.NICE is proud to announce three new Enlighten solutions to empower all CX stakeholders:Enlighten Copilot: Centralized conversational AI assistance that promotes smarter guided interactions, AI-driven personalized coaching, and task automation opportunities, creating better agent and supervisor experiences.Enlighten Autopilot: A new consumer-facing conversational AI solution based on trusted company knowledge, aligning responses with business goals, creating fully personalized experiences.Enlighten Actions: Unleashes unprecedented power to orchestrate your CX business, proactively uncovering areas for AI-driven optimization and carrying out complex automation to accelerate execution for all CX leaders.With Enlighten, NICE is the first to introduce generative AI capabilities specifically tailored for the CX industry, allowing service organizations to increase their decision velocity, drive skilled labor amplification, and create personalization at scale.This is a historic day for CX innovation with the launch of a comprehensive solution combining conversational AI with CXone’s unmatched breadth and depth of data, applications, and workflows, empowering trusted conversations to create exceptional experiences. |

At Techstrong Con 2023, digital transformation leaders will dig into top digital transformation trends for 2023, the key components of an effective digital strategy, how digital transformation has changed the way we do business and how to fully reap the benefits of digital transformation.
Join us to learn about:
- Security’s role in digital transformation
- How to leverage the cloud, IoT, AI, ML and other technologies to ramp up your digital transformation
- The benefits and dangers of the Metaverse
- How to harness the power of sustainable cloud storage
- Digital resilience as a digital transformation KPI
Monday, February 13th | 1 pm ET
Cybersecurity teams remain chronically overworked and short-staffed. It’s clear that AI must play a role in augmenting these cybersecurity teams, but there’s still a long way to go before AI models help level the playing field between cyber attackers and defenders. Many of the routine analytics tasks that are performed manually today will increasingly be automated, which will increase the amount of time teams have to discover and thwart more sophisticated threats. And AI has a role to play in cybersecurity hiring and talent retention, too—savvy cybersecurity professionals may not want to work for organizations that don’t invest in the AI technologies that can help them succeed. Register here.
Are you curious about the future of AI and how it will change everything? From ChatGPT to Stable Diffusion to Midjourney and more, join us as we dig deep into the promises and possibilities of the technology, as well as ethical and privacy considerations and how it will change the future of work. With generative AI poised to change the way we create and consume art and media, how we learn and how businesses scale and grow, it’s important to gain a deeper understanding of one of the most exciting technologies of tomorrow. Register here.
Join thousands of data engineers, data scientists and data analysts from around the world at this year’s Data + AI Summit. Save $200 off the price of a full conference pass — register by February 28 to take advantage of our early bird discount.
Discover the future of the lakehouse with keynotes from the co-founders of Databricks — CEO Ali Ghodsi, Chief Architect Reynold Xin and Chief Technologist Matei Zaharia.
In addition, explore our extensive onsite training and certification program. Register for the conference, sign up for training in San Francisco and test your skills with a free certification exam! You can also save 30% on all paid courses with discount code ET-TRAIN30
DevOps Webinars 2023
DevOps is Now DevSecOps!

Thursday, May 11th | 1 pm ET
APIs are the heart of many modern applications. They enable organizations to create new business models and methods of engagement. Yet, security breaches have increased due to the proliferation of unprotected APls and API endpoints. A survey conducted by Salt Security in 2022 found API attacks increased by 681%. A comprehensive API protection strategy can help address these challenges, but it must include discovery, detection and protection.
We’re excited to announce DevOps Connect: DevSecOps is back on April 24, as part of the RSA Conference 2023!
Join us at DevOps Connect: DevSecOps at RSAC 2023 as we explore different ways to effectively integrate security into DevOps processes, discuss the emergence of security engineers in DevOps and explore the role of developer security champions.
We’ll take a look at the latest DevSecOps trends, best practices and technologies, while focusing on two main topics:
- Shift left versus shift right security
- Open source security
Register for the RSA Conference 2023 and select any pass level to access our exclusive in-person event. Use code 5U3CYBVENXPO to obtain a FREE Expo Pass!
For more information, visit the DevOps Connect website.
Monday, January 23, 2023
3 p.m. ET | 12 p.m ET
Kubernetes allows developers to more easily manage containerized workloads and services with faster deployment, hardened security, and dynamic scaling and optimization. But how can you most effectively use this open source platform (commonly accessed via the Google Kubernetes Engine environment) with a service like MongoDB Atlas, which requires Kubernetes to have specific MongoDB domain knowledge?
In this presentation, MongoDB developer advocate Joel Lord and Google Cloud developer advocate Mofizur Rahman will walk you through the benefits of containerization and Kubernetes and how you can use the MongoDB Atlas Kubernetes Operator to manage the data services in your apps that have been built through MongoDB within GKE.
You’ll learn the benefits of containers and Kubernetes, get a demo of how to deploy an application with GKE and the Atlas Operator and learn about the many use cases where the Operator can streamline development, including network peering, database role management, database auditing, cloud backup and more.
After this presentation, attendees will have the opportunity to ask our experts questions in a dedicated Q&A.
The live webinar (20-min presentation followed by Q&A) will focus around Kubernetes:
- Containers and Kubernetes for DevOps
- Container orchestration with GKE
- MongoDB Atlas Kubernetes Operator
- Deploying an application with GKE and the Atlas Operator
The Best Growth Marketing Conferences to Attend in 2023
While many annual growth marketing conferences haven’t announced their 2023 dates yet, a number of them have, and it’s never too soon to register and book travel and accommodations.
- Traffic and Conversion Summit Sep 12–14, 2023, San Diego, CA, USA (+ Virtual)
- GrowthHackers Conference 2023 San Francisco, CA, USA (+ Virtual)
- MozCon 2023 August 7–9, 2023, Seattle, WA, USA
- Growth Marketing SUMMIT 2023 June 22nd, 2023, Alte Oper — Frankfurt am Main, Germany
- SXSW (“South by Southwest”) Startups Track 2023 March 10–19, 2023, Austin, TX, USA
- Confab Content Strategy Conference 2023 April 30 — May 3, 2023, MINNEAPOLIS, MN, USA
- HubSpot’s Inbound 2023 September 5–8, 2023, Boston, MA, USA
WhereScape Events January 2023:
- Why Data Vault is Worth the Investment? Dan Linstedt, the inventor of Data Vault 2.0, shares his experience and expertise in explaining why Data Vault 2.0 is worth the investment in time and resources. Feel free to register and join us on Thursday, January 25 at 18:00 AM CET.
- From Azure SQL to Azure Synapse – Jan 26, 2023
Best of 2022:
NEED to KNOW
Market Insights/Opinions, Business News/Headlines, Recent Research, Tech Innovation, Education, Events, FAQs and More
Crypto
Crypto vs Real Estate with Jason Rash

(courtesy of TradingView)
Digital Marketing Week Ahead 11 Dec ’22
- SEO PowerSuite Blog – SEO in 2023: 8 Trends and Predictions
- Google Ads gives in to organic search
- Featured snippets and zero-click results
- E-A-T remains important
- AI content overuse
- Entities take over keywords
- Google Shopping expanding
- Visual search becomes widely used
- AI-generated images get popular
Inriver recognized in the Gartner Market Guide for PIM Solutions:
The PIM solutions available today have matured to a point that they now offer standard capabilities such as digital shelf analytics (DSA), content optimization and generation, previously considered the remit of PXM solutions. What differentiates these vendors today is the additional capabilities they provide.Source: Gartner, Market Guide for Product Information Management Solutions
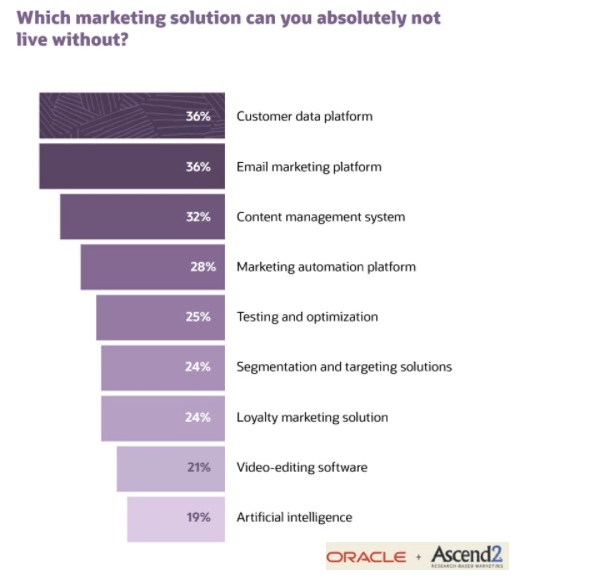
Hubspot: State of Inbound Marketing Trends 2022
- The data revealed that influencer marketing will continue to rise,
marketers should invest in short-form video, and content audits
should be part of every marketing org’s strategy.
- Short-form video content like TikToks and Instagram Reels are the most effective type of social media content
- Videos are the top content marketing media format for the third year in a row
- Social media is the #1 marketing channel in 2022
- Instagram, YouTube, and Facebook are the top 3 social
- media platforms marketers are using in 2022
- 83% of marketers believe it’s more effective to create higher quality content less often
- Facebook has the best ROI for social media ads versus other platforms
Cloud-Native Week Ahead 11 Dec ’22
- JupyterOne Security Leaders Debate: Cybersecurity Predictions for 2023
- Techstrong Con
- How digital transformation has changed the way we do business
- How to leverage the cloud, IoT, AI, ML and other technologies to ramp up your digital transformation
- Digital resilience as a digital transformation KPI
- Security’s role in digital transformation
- How to balance speed, security and innovation

| Date: 13th December 2022 Time: 9am GMT | 10am CET |
| Agenda [GMT] 9.00am- 11.45am- Welcome and introductions – Introduction to the Azure Databricks Lakehouse – Delta Lake: Data Reliability & Performance – Unity Catalog: Fine Grained Governance for Data & AI – Break – Data Engineering & Streaming – Databricks SQL & BI: Data Warehousing – End-to-end Data Science and Machine Learning – Wrap Up and Q&A |
- Palo Alto Networks
- Blog: Protect every connected device with Zero Trust IoT security, tailor-made for medicine.
- Security at the Speed of Code Case Study – Prisma Cloud’s shift-left capabilities gave Iron Mountain visibility from code to multi-cloud.
- At DevOps Asia Summit 2023, top industry leaders will come together to talk about their digital transformation journeys and how they have successfully implemented DevSecOps, SRE and VSM practices within their businesses to deliver high-quality software faster.

- Container Journal Webinars
- the tips and insights to ensure scaling Kubernetes doesn’t require compromising on the security and reliability of the environment. You’ll learn:
- How to address the security concerns of adopting Kubernetes
- The importance of setting up guardrails to protect DevOps professionals (from themselves)
- Ways to streamline Kubernetes’ auditing and cost management requirements
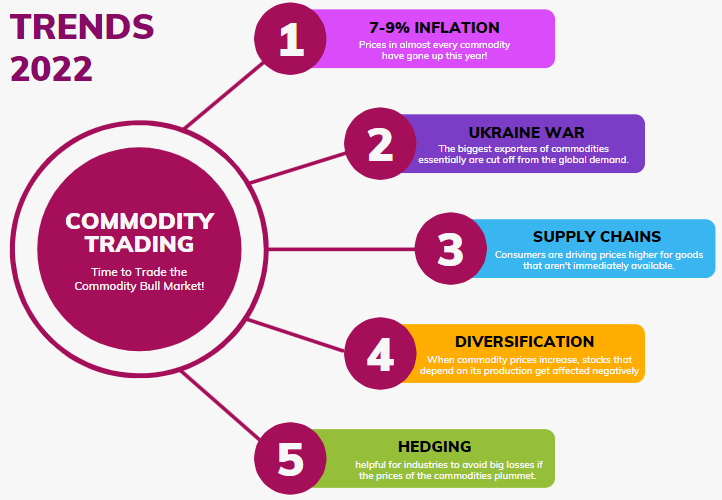
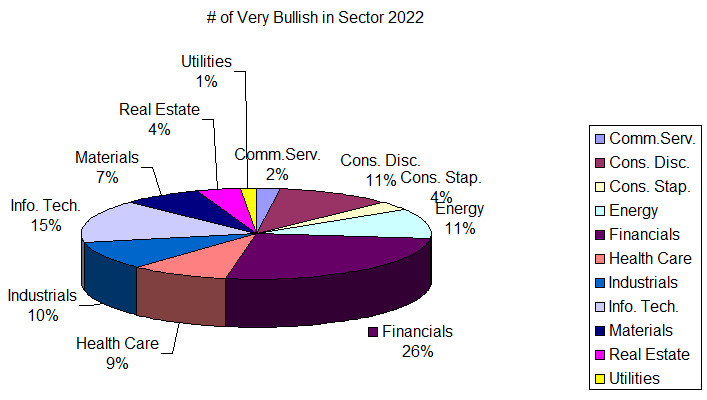
#StocksToWatch Wed 23 Nov ’22
- Tech layoffs: The trend of layoffs in the tech sector continues. Layoff pressure is building, with a weekly record number of layoff news on Bloomberg, following the notable headlines from META and AMZN,” BofA said. “Monthly new job postings have plummeted YTD, down 30% for the S&P 500 (SPY) YTD, led by high-paying jobs in Tech (XLK) and Financials (XLF): Comm. Svcs. (XLC) -63%, Tech -47%, and Financials -34%.” (18 comments).
- Inflation: September data for the two inflation readings paint two significantly different pictures: September CPI (year-over-year): +8.2% and September PCE price index (year-over-year): +6.2%. Both inflation readings are elevated and well above the Fed’s average 2% target. But it is often believed that the Fed’s hawkish stance is in an effort to get 8+% inflation down to 2%, but that’s not accurate. The Fed cares about the PCE price index. When you strip out food and energy, which is referred to as a “core” reading, the year-over-year inflation rate drops to 5.1%.2 Still a long ways to from a 2% average
EdTech Q4 2022
Google Cloud Training via edX:
Google Cloud Skills Boost + Innovators Plus
@googlecloud
Upcoming Tech Events of Interest
Virtual Zero Trust Security & Data Protection Hands-On Workshop on Tuesday, 29th November at 09:00 GMT.
- During this session, participants will learn about the HashiCorp security model which is predicated on the principle of identity-based access and security. In order for any machine or user to do anything, they must authenticate who or what they are, and their identity and policies define what they’re allowed to do.
- After an overview of Zero Trust Security, participants will go through a hands-on workshop using HashiCorp Vault to centrally store, access, and distribute dynamic secrets like tokens, passwords, certificates, and encryption keys across any public or private cloud environment. We will also introduce the concepts of Consul and Boundary and how together with Vault, these enable a Zero Trust Security model. This is a beginner’s workshop and no experience is required.
SB Webinar: Streaming data for DevOps, SecOps and ITOps
There is a tsunami of data flowing from networks, systems, applications and every other system that makes up your IT landscape. This data can give leadership teams valuable insights into your current technology environment as well as your ongoing projects.
However, there is a problem.
The data is coming too quickly; it is too complex and too voluminous for many technology approaches to fully support capturing all of it. In addition, the increasing costs of these systems as they scale can quickly outweigh their value. To balance visibility, scalability and costs, many organizations are forced to make tough decisions and only capture and retain snapshots of a fraction of their log data. The challenge with this approach is that you do not have a complete picture of your environment and limited insight when querying old data.
In this webinar, Mike Rothman, GM of Techstrong Research, will share findings from a newly released PulseMeter on creating a strategy to capture all of your log data. In addition, Arfan Sharif, technical marketing engineer at Crowdstrike, will discuss the business and technical challenges around capturing and analyzing data from across the enterprise and how to address these challenges to unleash the full value of log data.
During this webinar we will discuss:
- The challenges of collecting and storing all of your data
- How to collect logs from distributed environments
- The capabilities enabled by streaming data for DevOps, SecOps and ITOps practitioners
provides award-winning, affordable cybersecurity that grows with your organization. Get next-generation security in minutes, and protect your business against
– breaches
– ransomware
– malware, and more
CJ Webinar: 2023 Kubernetes Road Map
Kubernetes may have been around for the better part of a decade, but the platform itself continues to evolve. Heading into 2023, it will be imperative for organizations to keep track of what functionality is added and what is deprecated so they can effectively manage their fleets of Kubernetes clusters. After all, the only thing more challenging than managing Kubernetes itself is managing multiple clusters running multiple versions of Kubernetes that are dependent on outdated or no-longer-used APIs.
Thankfully, the Kubernetes roadmap provided by the Technical Oversight Committee provides some critical insights that IT organizations can use to better plan their Kubernetes cluster management strategy for 2023. Of course, if they choose to ignore the roadmap, they will be doing so at their own peril.

PaloAltoNetworks Upcoming Event:
Start the Clock Now
Three words are often associated with a zero-day attack – vulnerability, exploit and attack.
Given that no software patch exists for a zero-day vulnerability, it’s a tempting target. Once an exploit is created, an adversary can use it to carry out a zero-day attack. What happens then?
Join us for a special edition of “Race Against Time,” a simulated attack scenario spotlighting the critical steps SOC teams need to take in the first hours of a zero-day exploit.
You will learn how to effectively counter zero-day attacks at any stage of the lifecycle, including:
— Discovering a vulnerability
— Stopping an exploit in its tracks
— Responding to an actual attack.
Don’t wait. Register today.


Predict 2023 will look at what the upcoming year and the near future will hold in the realms of DevOps, digital transformation, cybersecurity and cloud-native. Prominent industry leaders and visionaries will share their speculations on what the future looks like and lay out a roadmap to success. Will 2023 be the year we reach a plateau of productivity? Will it be a hallmark year with a great level of disruption?
The fifth annual Predict conference is being led by our Techstrong Research team. This year’s agenda will be entirely live, featuring interactive panel discussions to prepare you for the new year ahead and beyond.
For more information, visit the Predict 2023 website.
Coming Up This Tech Week (W, 12 Oct. ’22)
The Databricks Migration Labs Week
- More and more organizations of all sizes, across multiple industries, are migrating their legacy analytics platforms to the cloud. Many of these companies are moving to the Databricks Lakehouse.
- The Databricks Lakehouse platform is designed to accelerate innovation, enhance productivity and manage costs more effectively, with faster, more efficient infrastructure and DevOps.
- In this series of three webinars, the Databricks team, in collaboration with its partners Microsoft Azure and Avanade, will share best practices and successful strategies for migration to the cloud and to the Databricks platform.

25 October – Hadoop, 26 October – ETL, 27 October – Data Warehouse
25 October, 12pm BST I 1pm CEST
Hadoop Migration with Databricks, Microsoft Azure & Avanade
In this webinar, you’ll learn why successful organizations are switching to modern, cloud-based platforms like Azure Databricks to drive innovation, productivity, and business outcomes. Leave with a best practice framework for safely and securely migrating data and workloads to Azure.
Key Expected Learnings:
- How companies drive business value with cloud-based data and analytics
- How to use the new model of unified capabilities in data engineering and analytics
- How to plan and structure a migration project to minimize risks and delays
=> You’ll get to discover the Avanade Brickbuilder Solution: Legacy System Migration by Avanade, developed by Avanade and powered on the Databricks Lakehouse Platform.
26 October, 12pm BST I 1pm CEST
ETL Migration
In this session, Databricks team will expose the ways and the tooling to migrate your ETL and business logic to Databricks Workflows.
Key Expected Learnings:
- What is Databricks Workflows and why you should care
- How to build a declarative and metadata-driven ETL in Databricks
- How to migrate your orchestration logic using an automatic approach
27 October, 12pm BST I 1pm CEST
Data Warehouse Migration
In this session, Databricks team will present both the best practices and the tooling to migrate from any enterprise data warehouse to the Databricks Lakehouse.
Key Expected Learnings:
- Why Databricks Lakehouse is the best fit for your BI workloads in the cloud
- How to build your data model, for both performance and governance, in the Lakehouse
- How to migrate your code using an automatic approach
- BrightTalk Weekly Update
Harnessing Data for Effective Customer Relationship Management in a Fintech
How to make an AI implementation happen…
Blocking Advanced Web Attacks with a Next-Gen WAF
Digital Currency and Private Blockchain: The Combo You Need for Your Business
The Great Data Migration: Cybersecurity & Privacy in M&A & Legacy Data Migration
- IT GRC Forum CPE Webinar: Streamlining GRC Controls to Optimize Cybersecurity November 17th @ 1pm ET
- DevOps.com
Driving Organizational Success With the 2022 State of DevOps Report
Latest DORA Report From Google Surfaces Raft of DevOps Challenges


Anti-Patterns Around Observability
Measure What Matters: Pick the Right Metrics That Tell Your Success Story
Introduction to Developer Observability
- Digital Shadows Weekly Intelligence Summary
ProxyNotShell spells déjà vu for MS Exchange Server defenders
Microsoft has acknowledged two zero-day vulnerabilities, dubbed ProxyNotShell, in its Microsoft Exchange Server software, versions 2013, 2016, and 2019. One of the flaws, CVE-2022-41082, can be exploited for remote code execution (RCE), but both flaws have been chained together in a few targeted attacks. Based on analysis, Microsoft has determined that a single, likely state-linked group is responsible for exploiting the flaws. Steps to evade exploitation are not foolproof; sophisticated threat actors will likely work around them. Defenders and cybercriminals alike eagerly await a proof of concept (PoC) exploit. Until a patch is available, organizations must take other defensive actions to avoid the type of mass exploitation experienced with the “ProxyShell” vulnerabilities.
E-Discovery Day Dec ’22
E-Discovery Day is on December 1st.

SIGN UP FOR THE E-DISCOVERY DAY NEWSLETTER
Powered by Exterro, EDRM, and ACEDS.
BrightTalk Weekly Oct ’22
- IT GRC Forum: CPE | Data Privacy Essentials Nov 03 2022, 6:00pm CET
- Cybersecurity Insurance and MFA: What You Need to Know Oct 05 ’22, 2:00pm CEST
- Enabling Successful Recovery from a Ransomware Attack Oct 05 2022, 6:00pm CEST
- The Top 5 Cloud Native Risks Oct 04 2022, 4:00am CEST
- The Power of SIEM Oct 04 2022, 11:00am CEST
Just happened:
Mastering the Message: How Marketing can “Install” Messaging
The Tell-tale Signs of a Network Compromise: A Stage-by-Stage Attack Chronology
Secure Your Cloud Environment from Evolving Threats
DevOps Weekly Oct ’22
This month’s topic spotlight is DevOps at the edge. Edge computing could be tech’s next trillion-dollar opportunity, and your organization could thrive if you’re ready to take advantage of it.
Gartner® predicts that ”By 2025, more than 50% of enterprise-managed data will be created and processed outside the data center or cloud.”
Digital transformation is pushing enterprises to be more distributed and expand to the edge. I&O leaders must plan for the growth of IoT and related data at the edge, protect their enterprise from edge growing pains in security and connectivity, and prepare for changes in edge computing use cases.
- Edge Computing: Tech’s Next Trillion-Dollar Opportunity
- Is Your Infrastructure Ready for Edge Computing?
- Getting Started With K8s at the Edge
- White House Releases Software Supply Chain Security Guidance
- Inclusive Design: 5 Areas of Focus

- Beyond core cloud primitives such as compute instances, storage and networking, DevOps professionals crave security products, edge computing power, content delivery and more from their cloud provider.
- Attend this webinar to hear the latest 2022 DevOps and the Public Cloud research from Techstrong Research.
Tech Weekly Sept ’22
IT GRC Forum via BrightTalk Online Event:

About this talk
In today’s interconnected world of rapid data exchange, GRC Controls impact each and every part of an organization’s cybersecurity posture. Yet, despite this, countless organizations still take a siloed, reactive approach to GRC, often playing a constant game of catch-up. Not only are these businesses likely to miss things, but their approach to cybersecurity is often poorly optimized and they’re spending far more than they need to, investing in outdated manual processes to deal with overlapping requirements. On this webinar, we will discuss how to streamline GRC controls and optimize cybersecurity risk management processes, to enable leaders to determine what investments best reduce risk with the best return on investment (ROI). Attendees will learn how to: – Simplify GRC and security operations by reducing the number of controls your organization has to deal with, therefore reducing its workload to test and audit the controls – Develop a set of controls baselined to the internal and external requirements that your organization needs to meet – Enable both security process automation and enterprise risk decision-making – Shrink your organization’s cybersecurity attack surface
Upcoming Techstrong Security Event of Interest:

- Snowflake is making massive moves to build its cloud data sharing, predicated on an expanded CY26 TAM of $248B.
- Apple‘s unchanged pricing suggests steady profit margins, Apple Services remains the key to high single-digit margin and sales expansion, pushing operating margins closer to the 30% mark.
- Shopify is a mission-driven and founder-led company that has beat the stock market since IPO until 2022 started, it has an end-to-end business model and ecosystem that merchants can take advantage of to scale
- DevOps Workshop: ML-Powered SOlutions for AWS
Tuesday, September 27, 2022 1 p.m. ET
As IT infrastructure consistently churns out record amounts of new data, ITOps teams often struggle to manage and analyze it with traditional tools. A new approach is needed to help IT shift from reactive to proactive management of incident resolution data to boost application availability, save time-to-detect and resolve the most critical issues and lower costs. Join this hands-on workshop for a live presentation and interactive lab and learn how you can leverage Amazon DevOps Guru, a fully-managed AIOps solution from AWS to detect, diagnose and optimize the performance of your infrastructure.
You will learn how to:
- Proactively monitor and optimize your databases for performance bottlenecks and operational issues
- Easily trace and resolve serverless application performance issues with ML-powered insights
- Reduce time-to-resolve operational issues from days to minutes
JONATHAN VOGEL
Developer Advocate – Amazon Web Services
Marketing Digest Sept 2022
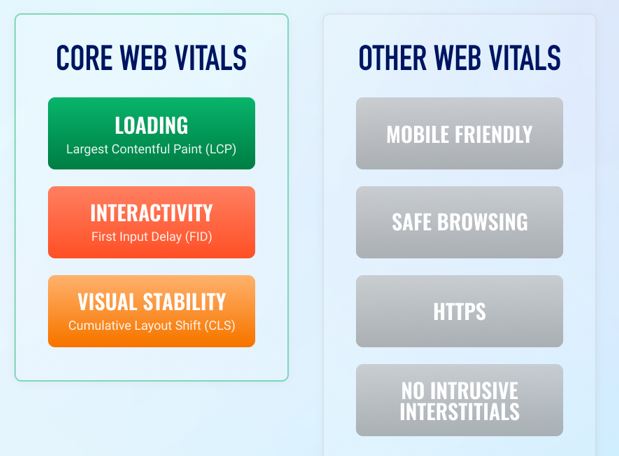
- Core Web Vitals have been part of Google’s ranking algorithm for almost a year.
- Core Web Vitals (CWV) are a set of metrics that help Google assess the overall performance of a webpage. These three metrics are:
- Largest Contentful Paint (LCP)
- First Input Delay (FID)
- Cumulative Layout Shift (CLS)
- Page Speed: SEO Guide to Shorter Load Times
- Read more: New Ranking Factors: Core Web Vitals
HubSpot Niews:
- 8 Steps to Launching an Online Learning Academy Your Customers Will Love
- Facebook is Redesigning its News Feed: What Marketers Need to Know
- Are Recession Concerns Already Impacting Consumer Spending Habits? [New Data + Takeaways for Marketers]
Medium Better Marketing:
- 10 SEO Tools To Level Up Your Marketing in 2022 (Free & Paid)
- Build your own AI-powered content generator with 7 lines of Python code
- 3 Simple Ways to Make Extra Income with a Faceless YouTube Channel
- Here Are 5 Advantages of Running Newsletter
- Customers Profiling Using K-Means Clustering
Explore More:
- 10 AI-Powered Websites for Content Writers
- Marketing Summer 2022 Update
- HubSpot TikTok Marketing 2022
- Simple E-Commerce Sales BI Analytics
- A K-means Cluster Cohort E-Commerce
- Telco Customer Churn/Retention Rate ML/AI Strategies that Work!
- 20 Top Social Media Sites
- Brand Architecture: Google vs. Amazon
- Content Marketing
- Pilots: MarTech
- Promo
- Nonprofit
- Community
EdTech Update Aug 2022
- Grow your career by earning your Bachelor of Science in Marketing from the University of London. You’ll gain the knowledge and experience necessary to succeed in marketing management, strategy, design, and analyst roles as you build the leadership and interpersonal skills employers are looking for. Key areas include environmental sustainability, fair and equitable global economic growth, gender and racial equality, and ethical approaches to consumption.
- University of California, Irvine invites you to explore their Coursera offerings, or see what the Division of Continuing Education (DCE) has to offer such as:
- Certificates – over 60 online career-oriented programs in areas such as business and leadership, law and finance, technology, healthcare, life sciences, and engineering
- Technology Bootcamps – coding, data analytics, cyber security, and digital marketing
- International Programs – ESL, academic study abroad, and accelerated certificate programs held on the beautiful UCI campus
Recommended Data Science Guided Projects:
Explore “data science for business” courses
- Data Analytics for Business
- MACHINE LEARNING: PRACTICAL APPLICATIONS
- AI and Data Analytics for Business Leaders
- UC Berkeley School of Information’s online Master of Information and Cybersecurity (MICS) program
- DIGITAL MARKETING: A STRATEGIC PERSPECTIVE – Yale School of Management
Logistic Regression Practical Case Study: Breast Cancer detection using Logistic Regression
- Natural Language Processing (NLP) with BERT: Movies reviews Semantic analysis using BERT
- DevOps – The Introduction Course: The Swiss Army Knife of DevOps and Cloud courses. Introduced basic DevOps concepts to an Absolute Beginner
Python for Finance: Enroll in our Python for Finance course today! Learn to use various Python libraries such as QuantConnect to perform financial analysis and research.
Deep Learning with Tensorflow and Keras: Enroll in our Deep Learning with Keras and Tensorflow Course! Learn how to use Python for Deep Learning with Tensorflow 2 and Keras libraries. Start today!
Computer Vision with Python and OpenCV: Take our Computer Vision course to learn OpenCV! In this course, you’ll use the OpenCV Python library to process and analyze images and video data.
Cybersecurity Update July 2022

we explore the rapidly evolving application and API landscape and offer concrete ways organizations can protect against threats to their application code, APIs and related components.
AT&T Cybersecurity White Paper:
Cyber Risk Reduction in the Era of Accelerating Digital Transformation
Increased use of cloud services, edge computing, and greatly expanded remote working options have all increased the level of cyber risk for organizations that aren’t always evident. As digital transformation initiatives accelerate, an organization requires a deep and accurate understanding about its cyber risk.
An organization-wide risk assessment profile should be completed to identify critical assets, functions, and business processes that need protection. Throughout the risk assessment, security maturity should also be assessed across all five organizational pillars to avoid cognitive dissonance regarding the level of maturity an organization has achieved.

The explosion in cloud adoption, digital transformation, and remote work – combined with a never-ending amount of phishing and ransomware attacks – are shaping the evolution of threats. But it’s difficult adapting security strategies to mitigate risks, especially given the varying skillsets that exist within an infosec team, burnout, competing priorities, and a lack of visibility into blind spots.
In this Fireside Chat, Melinda Marks, Senior Analyst at ESG, and Jason Steer, CISO at Recorded Future, explore the top security trends you should keep top of mind, how you can use threat intelligence to stay 10 steps ahead, and much more.
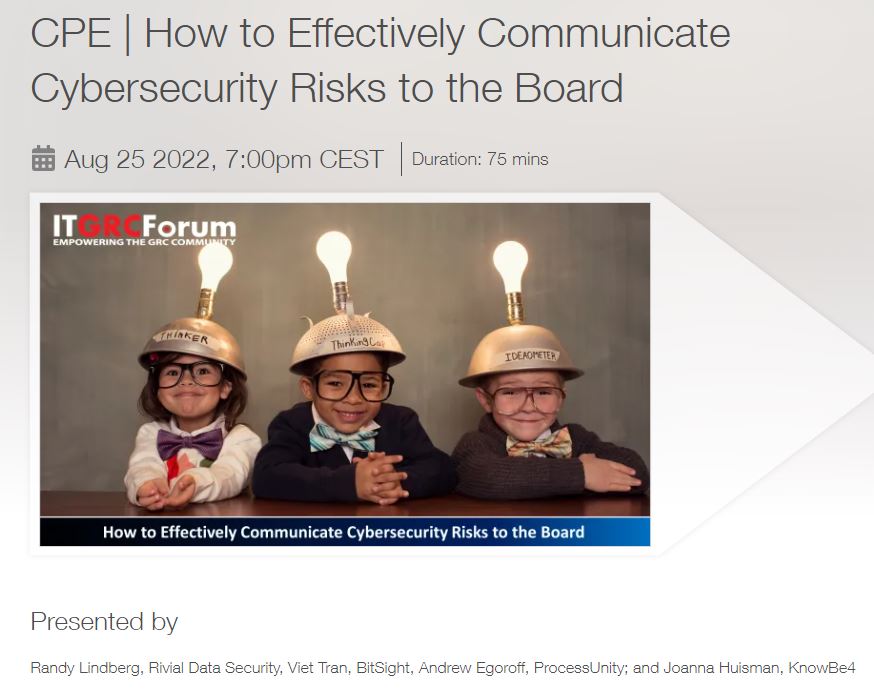
It has always been challenging for security leaders to communicate the value of cybersecurity investments to board. Giving transparency about the weakness of organizations can be pretty uncomfortable but, it is essential to increase the Cybersecurity level. As an IT Manager, CISO, or CSO, your understanding of risk and compliance is intimate and understood in infosec terminology. You must offer board executives a set of data to help them make informed decisions based upon the optimal management. However, the Board of Directors expect brevity, and examine business practices from a birds-eye perspective. Attend this webinar to learn how to improve your board’s cybersecurity posture by effectively communicating risks in business terms, including how to: – Create trust with dialogue delivery and engage leadership with universal, non-security terms – Show metrics to quantify challenges, & categorize in financial terms – Use data to explain the problem, and share how that same data provides you with a way to solve it – Help board executives move to an ‘internet everywhere’ approach.
DevSecOps Monthly Picks July 2022
Honeycomb: Organizations have practiced application performance management and monitoring for as long as there’s been software. Over the years it has evolved and changed to accommodate different methodologies like Agile, but traditional monitoring and testing can’t keep up with the new paradigms necessary for cloud-native applications built using containers and with microservices. That’s where observability comes in. As software architectures become more complex, observability has become an essential part of the testing environment to help identify and resolve issues early on in the development life cycle. Ultimately, testing and observability share the same goal: To make sure systems are running smoothly.
AWS Modernization Workshop with CircleCI: GKE Autopilot is a new mode of operation in Google Kubernetes Engine (GKE) designed to reduce operational costs around managing clusters, optimizing production time and driving higher workload availability. As a Google Cloud Platform (GCP) partner, CircleCI makes it easy to integrate CI/CD workflows with GCP and utilize modes of operation like Autopilot.
Legit Security / Takeda Pharmaceutical : How to shift security left
- Learn how to gain buy-in from development leaders to embed security into development
- Become familiar with modern software supply chain risks such as: hard-coded secrets risks, infrastructure-as-code risks, pipeline risks and SDLC misconfiguration risks
- Understand the value of fixing security issues before production
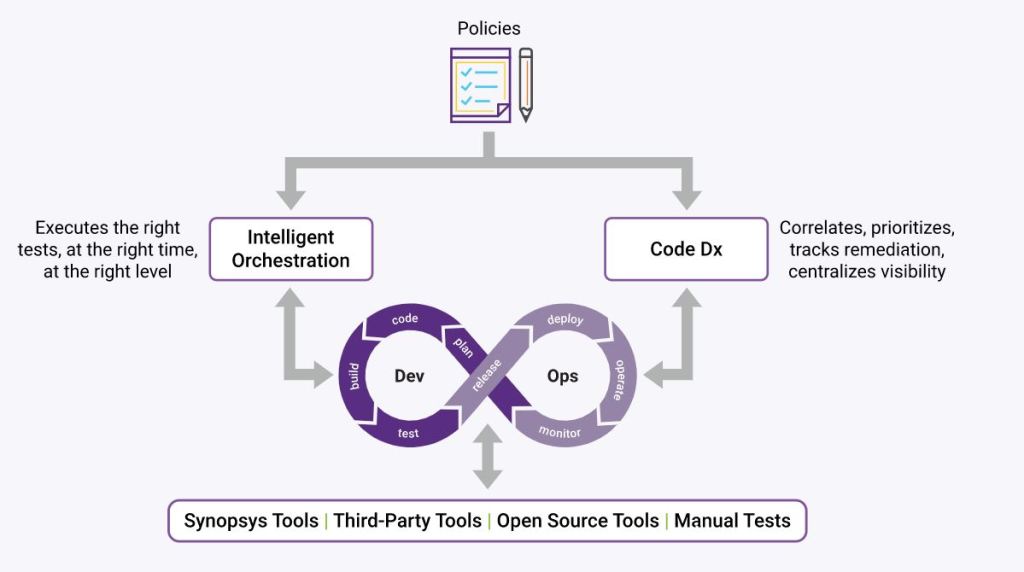
Synopsys: According to the 2022 Open Source Security and Risk Analysis (OSSRA) report, the overwhelming majority of software development organizations are leveraging open source to build their applications. However, the scale of use creates a growing management challenge. While development and risk management teams scramble to patch vulnerabilities, decipher complex license terms governing obligations associated with the use of each open source component and stay up to date with component versions, another consideration begs attention: How does this open source risk affect my software supply chain?
- What a software supply chain looks like
- How open source introduces risk to a software supply chain
- Applying the OSSRA findings to reduce your software supply chain risk.
Though we hope they won’t happen, disasters are inevitable—especially in today’s unstable world. Because your customers, your revenue and your reputation depend on your applications’ availability, it is essential to have a strong disaster recovery (DR) strategy in place.
But because many organizations are running containerized applications in distributed environments across multiple clouds and storage platforms, traditional DR solutions often miss the mark when it comes to protecting and recovering cloud-native applications. For example, when protecting Kubernetes applications, you need to be sure that application data AND metadata is quickly recoverable—you don’t want to be left stitching backups together when time is of the essence!
Learn how to create a disaster recovery strategy for your cloud-native applications, including how to:
- Continuously back up your applications and their associated data no matter what they contain or where they’re located
- Easily select backups from different repositories
- Specify namespace mappings
- Reconfigure application data and metadata across multiple applications at one time.
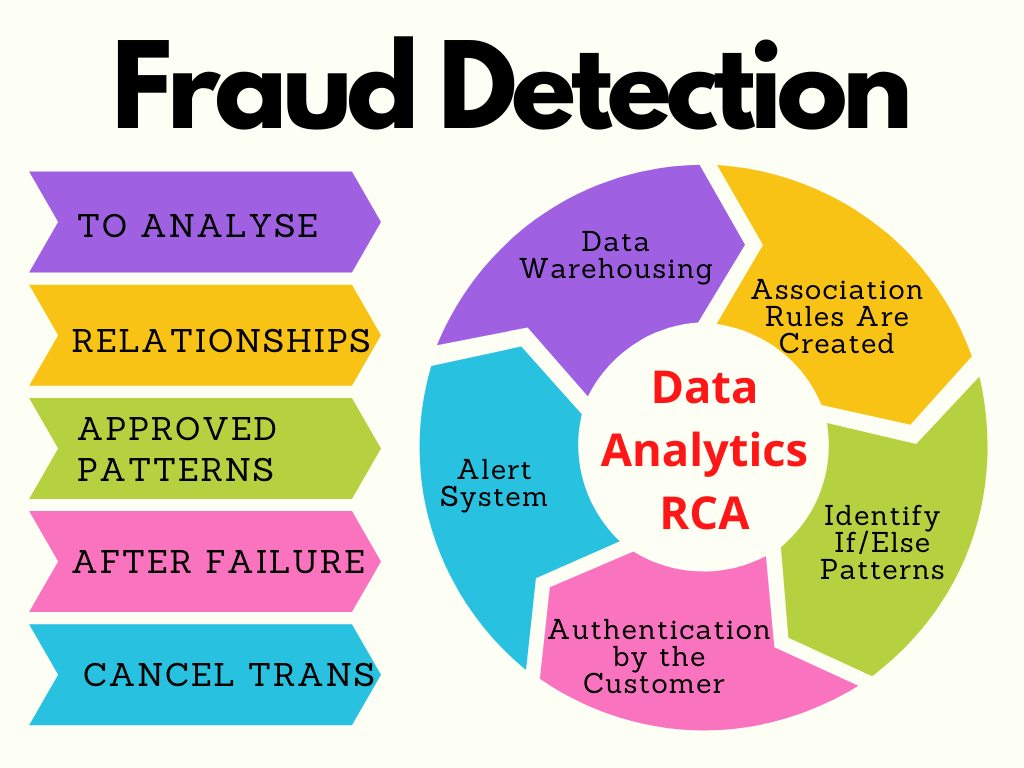
ML/AI Credit Card Fraud Detection
Q2 2022 Update
The Kaggle Credit Card Fraud Detection dataset (click here for the dataset).
Steps Involved
- Importing the required packages into our python environment.
- Importing the data
- Processing the data to our needs and Exploratory Data Analysis
- Feature Selection and Data Split
- Building six types of classification models
- Evaluating the created classification models using the evaluation metrics
This process leads to six different types of classification models such as XGBoost, Random forest, KNN, Logistic regression, SVM, and Decision tree. The models were evaluated using the evaluation metrics (confusion matrix, precision, recall, accuarcy score, and F1-score).
The key challenge is to handle the unbalanced dataset.
- RandomUnderSampling (RUS) — This method discards a random subset of the majority class, preserving the characteristics of the minority class, ideal when you have a large volume of data. This method can lead to lower performance when making predictions of the majority class.
- ADASYN — Generates new samples, close to the original ones, that are misclassified using a K-Nearest Neighbors classifier. To better understand this method, click here.
- SMOTE — The basic implementation of SMOTE, meanwhile, will not distinguish between easy and difficult samples to be classified, as is done in ADASYN.
Key Takeaways:
- Logistic Regression algorithms perform better when dealing with balanced data.
- Decision Tree algorithms were superior when dealing with unbalanced data.
- The ideal solution is the one that best serves the institution, and can be the one with the highest AUC or the one with the highest number of fraud detection.
- The algorithm that best predicted fraud was the Logistic Regression Model trained on balanced data using the ADASYN method.
Cf. GitHub Link to the complete project.
See Related Case Studies:
Data-Driven ML Credit Card Fraud Detection
Credit Card Fraud Detection — Part I
Tech Week Ahead Monday, July 11, 2022
Scalable Storage On-Prem for AWS Outposts Jul 12 2022
Achieving Business Value with Analytics Jul 12 2022
DevSecOps Topic Spotlight: Continuous Deployment (CD)
DevOps workflows are now more widely used than ever. Monitoring software and infrastructure performance and using continuous integration to automatically build and test code changes remain the most popular DevOps-related activities cited in the Continuous Delivery Foundation’s recent State of Continuous Delivery in 2022 report. While nearly half of developers (47%) said they used either continuous integration or continuous deployment platforms, only about 20% reported using both to automate all application build, testing and deployment.
The problem is that continuous deployment is much more complex and difficult to achieve than continuous integration. The number of organizations that routinely make use of a CD platform is still relatively small. Historically, each platform used to run applications has been unique, so automating delivery and deployment has been problematic. This month, we’ll focus on the end stages of the DevOps pipeline and explore continuous deployment and continuous delivery in depth, including the concept of CD-as-a-service.
Events

Kubernetes security is becoming more challenging as the number of clusters running cloud-native applications continues to multiply rapidly. Challenges range from allowing in only legitimate traffic and enabling least-privileged communications between services to defend against attacks moving laterally between clusters, to validating how a workload is operating within the expected guardrails.
It’s also often assumed that because a container only runs for a few seconds on a
Kubernetes cluster, it won’t be compromised. However, containers are starting to run for longer periods and are being used with stateful applications containing sensitive data. Organizations also are paying more attention to Kubernetes as they look to lock down software supply chains in the wake of a series of high-profile breaches.
As Kubernetes becomes ever-present in production environments, it is imperative that organizations understand and take appropriate steps against the threats. In this editorial webinar, our panel of experts will discuss:
- The state of Kubernetes security
- What organizations need to address with respect to Kubernetes security in production environments
- Who should be in charge of Kubernetes security in the age of shift-left


| Veeam Ransomware — Prevent, Detect and Restore |
| July 14, 3 p.m. CEST |



While thousands of customers are using serverless applications to access infrastructure and resources as they go, finding the right balance between the parameters for their function and the performance and availability of those functions is challenging. Join this hands-on workshop, featuring live presentations and interactive labs, to learn how you can leverage a fully managed AIOps solution from AWS to:
- Automatically identify and analyze a wide range of performance and availability-related issues for serverless applications
- Proactively detect application issues before a customer-impacting event occurs
- Receive ML-powered insights to manage and take real-time action on application issues

The Google Cloud Sustainability Summit brought together top industry leaders to explore the latest strategies and tools that can help solve the tough challenges of climate change.
Original air date: June 28, 2022 10:00 AM

Tuesday, June 28, 2022 3 p.m. ET
In this workshop, we’ll examine how Pulumi can rapidly accelerate provisioning of cloud infrastructure. We’ll focus on AWS Lambda and build an example set of microservices utilizing AWS’s newest Lambda features.
Attendees will be guided through the process of provisioning a set of example Lambda resources in AWS and see real-time examples of how Pulumi’s innovative programming model helps turbocharge cloud engineering.
Key Takeaways:
- How to provision a Lambda function in AWS
- How to provision infrastructure such as DynamoDB and API Gateway to support your microservice applications
- Learn how to take advantage of some of the newest Lambda features
Workshop pre-requisites:
Attendees should have the Pulumi CLI installed on their machines. Attendees should have access to an AWS account. To get started, go to https://pulumi.com/start
E-Training Opportunities
Coursera EdTech Update July 2022
- DevOps on AWS – Amazon Web Services 4 courses
- AWS Fundamentals: Addressing Security Risk 1 course
- Google Data Analytics – 8 courses
- IBM Full Stack Software Developer – 12 courses
- Introduction to Containers w/ Docker, Kubernetes & OpenShift (IBM) – 1 course
- Azure: create a REST API using NodeJS Serverless Functions – 1 course


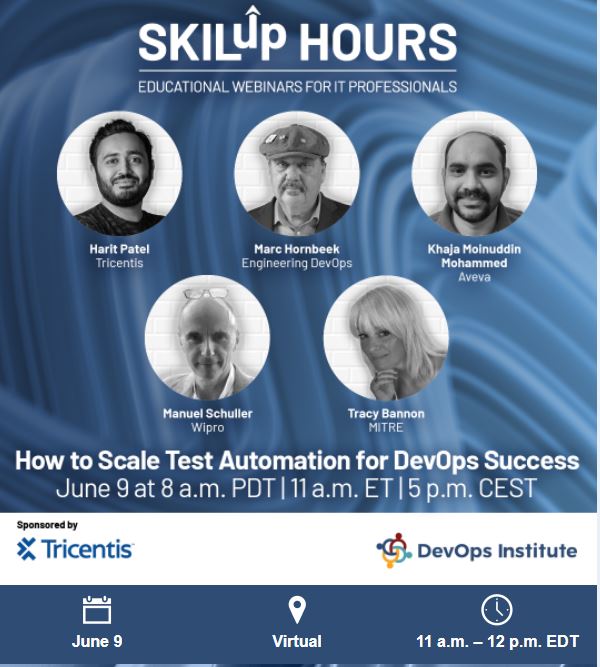
SkilUp Hours by DevOps Institute
SKILup Hour: How to Scale Test Automation for DevOps Success
June 9th, 2022
WEBINAR for AMERICAS/EMEA
8 a.m. PT | 11 a.m. ET | 5 p.m. CET
Coursera
- AI and Machine Learning MasterTrack® Certificate
- Digital Transformation Certificate
- Business Analytics for Managers MasterTrack® Certificate
Cybersecurity Monthly Update – May 2022
A Weekday Market Research Update
Coming Up This Week
Cloud, AI, DevSecOps
- 3 key elements of cloud-native initiatives in banking
- Securing Application Access with Virtual Apps and Desktops Service
- Navigating Sustainable Investment in a rapidly evolving economic landscape
- DevSecOps: How to Build Security into DevOps
- Bad Analytics: What They Are and How To Avoid Them
- Ensure customer trust with data automation and security best practices
- Accelerate IT Operations and App Development Across Distributed Infrastructures
- The Future of Business Intelligence
- 3 key elements of cloud-native initiatives in banking
- Securing Application Access with Virtual Apps and Desktops Service
- Navigating Sustainable Investment in a rapidly evolving economic landscape
- DevSecOps: How to Build Security into DevOps
- Bad Analytics: What They Are and How To Avoid Them
- Ensure customer trust with data automation and security best practices
- Accelerate IT Operations and App Development Across Distributed Infrastructures
- The Future of Business Intelligence
- Code-First Data Science Using DataRobot’s AI Cloud Platform
Hey there!
Hi, I’m Al, a digital accelerator and dog lover, passionate about fintech, ML/AI and social media marketing. Thanks for visiting!
First time to the site? Start here

Weekly Market-Beating Stock Ideas, Investing Trends, Analysis, Opinions, Debate, and More
Sources:
Zacks Investment Research, Inc.
Let’s hang out!
Make a one-time donation
Make a monthly donation
Make a yearly donation
Choose an amount
Or enter a custom amount
Your contribution is appreciated.
Your contribution is appreciated.
Your contribution is appreciated.
DonateDonate monthlyDonate yearly

Leave a comment