Featured image by Dan Nelson on Unsplash
Contents:
- Palo Alto Networks
- AT&T Cybersecurity
- DevSecOps Outlook
- Top 5 Cloud-Native Risks
- IT GRC Forum
- Snowflake Security
- Digital Shadows Digest
- ksqlDB Security
- AIaaS Data Security
- Related Online Events
- E-Training Opportunities
- Further Reading
Palo Alto Networks
Prepare to dive deep into the industry’s most comprehensive security orchestration
It’s time to level up your SOC skills with Cortex® XSOAR™!
- Join the industry’s premier event for SASE, September 2022. ZTNA 2.0 provides you a critical first step in accomplishing a successful SASE deployment and unlocking this next phase of growth for your organization.
AT&T Cybersecurity
- After stripping off all the flashy stuff that underperformed, the core of AT&T returns to offer reliable cash flow.
- Q2 results, despite the small cut in FCF, hit it out of the park with its best quarter for subscriber growth.
AT&T SASE Branch with Fortinet:
With the rise of cloud-based applications and tools to support new business initiatives, organizations with multiple branch locations are switching from legacy wide-area networks (WANs) to software-defined WAN (SD-WAN) architectures. SD-WAN offers faster connectivity, cost savings, and performance for software-as-a-service (SaaS) applications as well as digital voice and video services.
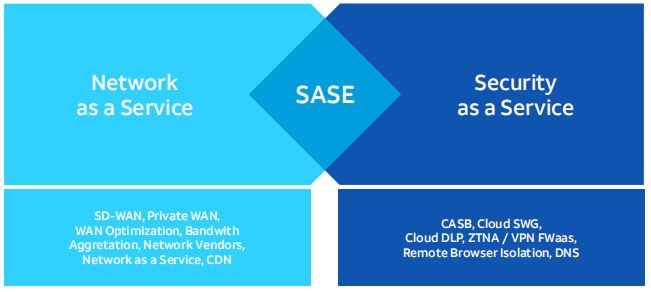
Secure Access Edge Access (SASE):
A unified, comprehensive approach to networking and security for the modern enterprise.
Adopting a single, cloud-delivered solution in place of disparate point products helps organizations:
- Reduce complexity
- Rapidly scale out remote workers and branch locations
- Deliver consistent security policy enforcement to all users, regardless of location.
What is more important, the reduction in complexity and overhead frees up technical, financial, and human resources to help businesses better position themselves for future opportunities and growth.

DevSecOps Outlook
DevOps.com webinars: Modern Data Protection With Metallic DMaaS: Hybrid, Kubernetes and Beyond Wednesday, August 24, 2022
With the acceleration of hybrid cloud adoption and digital transformation initiatives, data is in more places than ever. From containers and on-premises environments to cloud and SaaS-based applications, businesses need a smart strategy to protect their entire data estate from today’s threats. And while native tools provide businesses with high availability, they are not enough. In this session, Metallic’s CTO David Ngo unpacks the critical need for dedicated data protection, the advantages of purpose-built solutions and how Metallic DMaaS safeguards data from deletion, corruption and ransomware attacks no matter where your data lives.

- Learn how to identify key aspects of open source security
- Learn how robust security practices are actually possible in Kubernetes
- Understand the realities of today’s open source software and the real risks that all organizations and industry professionals should be aware of
- Learn what machine learning is and what place AI has in IT operations
- Understand how to establish a zero-trust profile for an application, as it makes its way across Dev/Test, Q/A and eventually to a production cluster.
Top 5 Cloud-Native Risks
- Application Vulnerabilities
- Infrastructure misconfigurations
- Malware
- Overprovisioned access
- Insecure APIs
Best Practices:
- Team mindset
- Reducing complexity with a platform approach
- Choosing cloud-native technology
- Automating security
- Gaining visibility across all data and workloads
IT GRC Forum
CPE Webinar: Utilizing the NIST Framework for Full-Cycle Privilege Orchestration Sept. 8 @ 1pm EST

Snowflake Security
The unique Snowflake design physically separates but logically integrates storage and compute along with providing services such as security and management. The cloud services layer manages data security including the security for data sharing.
Along with tables, Snowflake views are the primary objects maintained in database
schemas.
One purpose of views is to display selected rows and columns from one or more
tables. This is a way to provide some security by only exposing certain data to specific users. There is the ability for views to provide even more security by creating a specific secure view of either a non-materialized or materialized view.

Creating multiple layers of security that take advantage of Snowflake’s built-in security options is among the best practices for managing security.
Digital Shadows Digest
- On-Demand Webinar: Digital Risk Protection in a Modern Threat Landscape
- Data Leakage Detection Solutions Guide
- Detecting Fake Social Media Profiles | Case Study
- Dark Web Marketplace Trends
- Cyber Threat Intelligence Solutions Guide
- Vulnerability Intelligence Solutions Guide
ksqlDB Security
- ksqlDB supports several combinations of encryption and authentication on its client-facing and internal endpoints. ksqlDB also supports many of the security features of the other services it communicates with, like Apache Kafka® and Schema Registry.
- You can use ksqlDB with a Kafka cluster in Confluent Cloud.
- You can secure installations of ksqlDB outside of Confluent Cloud, like on-premises installations or manual installations on other cloud platforms.
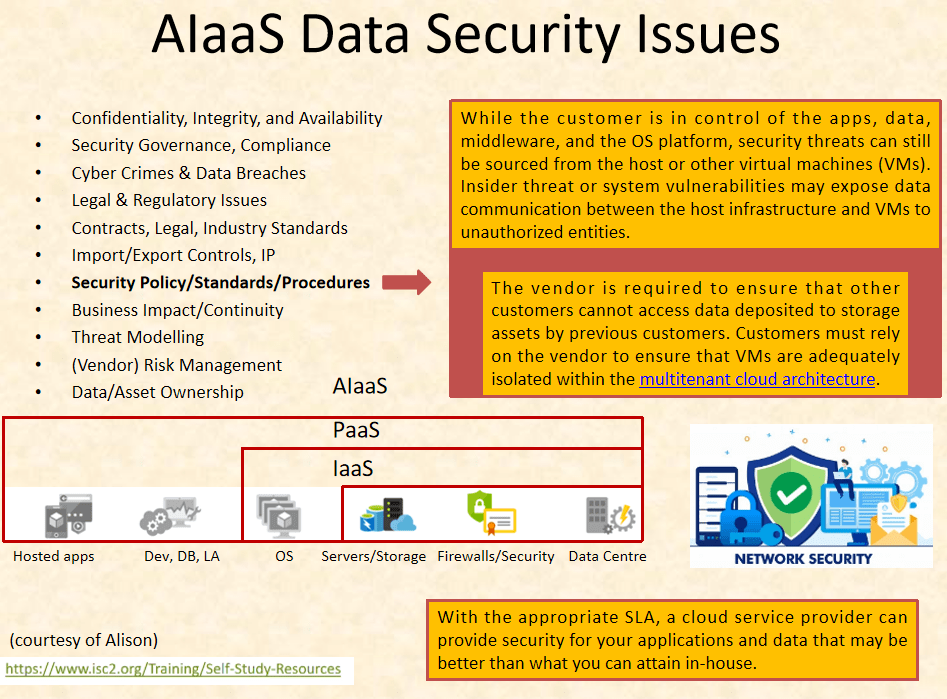
AIaaS Data Security
Related Online Events
- Outwit Attackers with a Proactive Cybersecurity Plan
- The Endpoint Security Gap: Are you leaving the door open to attackers?
E-Training Opportunities
- Cybersecurity MasterTrack® Certificate
- Cybersecurity Risk and Strategy IMD online program
- NIST – Cyber Security Framework (CSF) Foundation
- Introduction to Cybersecurity
- Cyber Security: From Beginner to Expert (2022)
Further Reading
Data-Driven ML Credit Card Fraud Detection


Leave a comment